网谷杯安全极客大赛2025-NewRC4のWP
题目描述
题目名称
NewRC4
题目难度
★★
题目分值
475
前置知识
1、查壳以及UPX脱壳
2、RC4加密算法
考察知识点
1、UPX魔改壳
2、RC4加密算法+魔改
解题工具
1、Exeinfo
2、010Editor
3、IDA
4、python3
解题步骤
第一步:题目信息
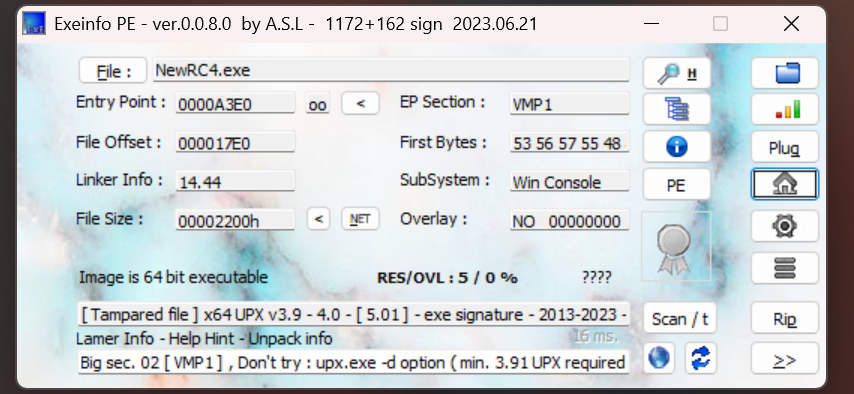
使用Exeinfo查看程序基本信息,发现了UPX压缩壳
第二步 :解题过程
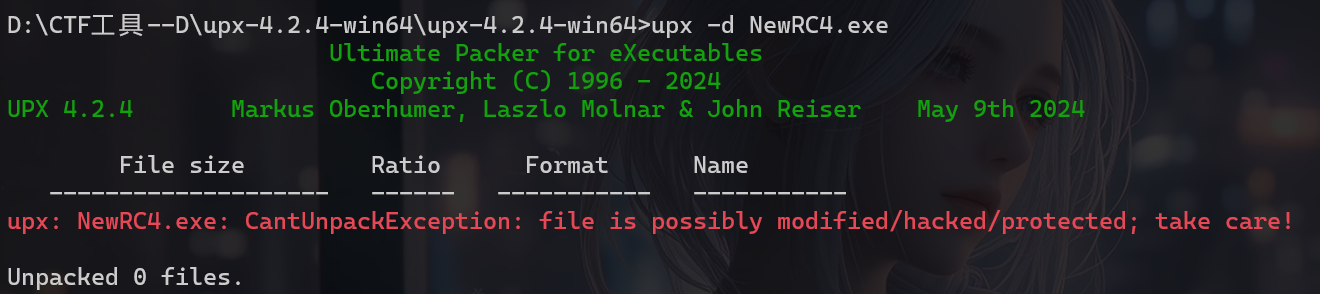
1、使用UPX尝试脱壳,发现报错
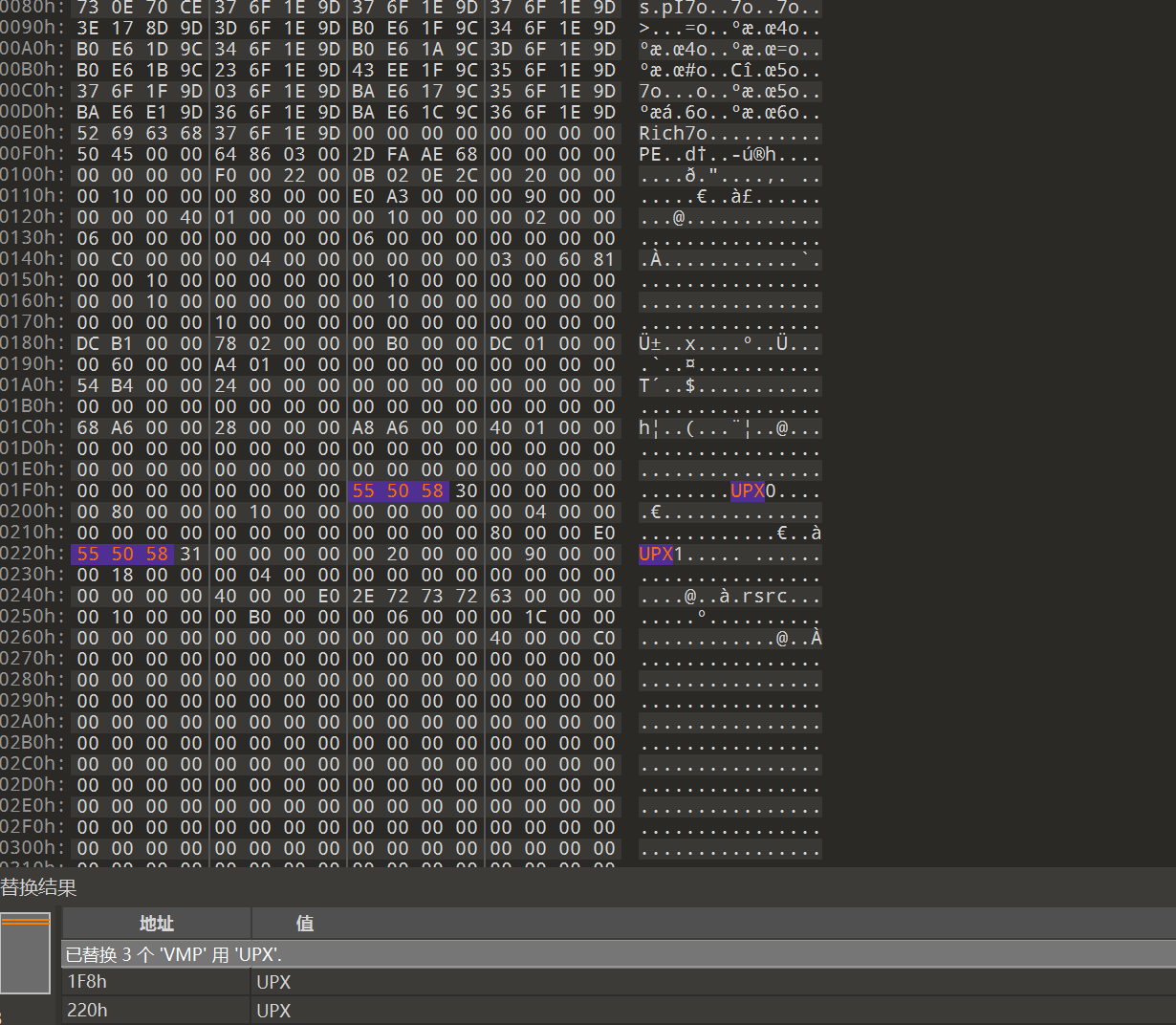
于是拖到010里面查看详细信息,看到原本应该是“UPX”的地方变成了VMP,把所有的VMP改为UPX,
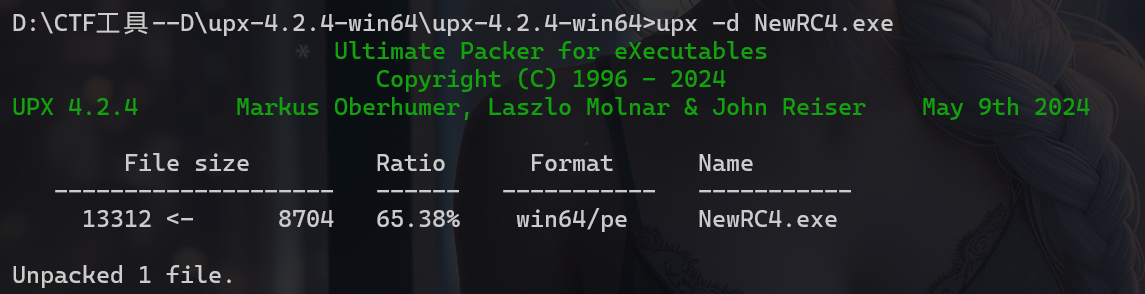
保存后再次尝试脱壳,成功脱壳
2、进IDA里查看,点进main函数
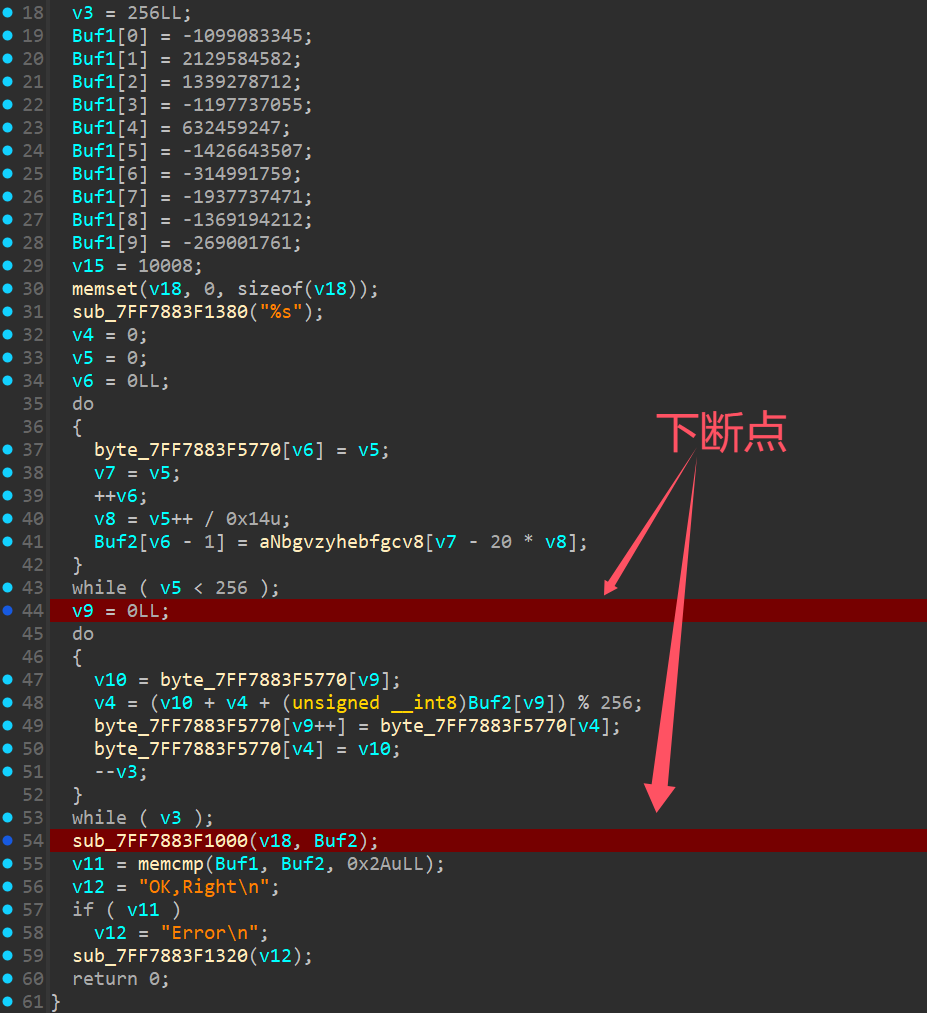
v3 = 256LL; |
通过v4 = (v10 + v4 + (unsigned __int8)Buf2[v9]) % 256;等相关特征分析是RC4加密算法,但是静态分析看不出sbox和key,于是尝试动态调试
在以下地方下断点,跑动调
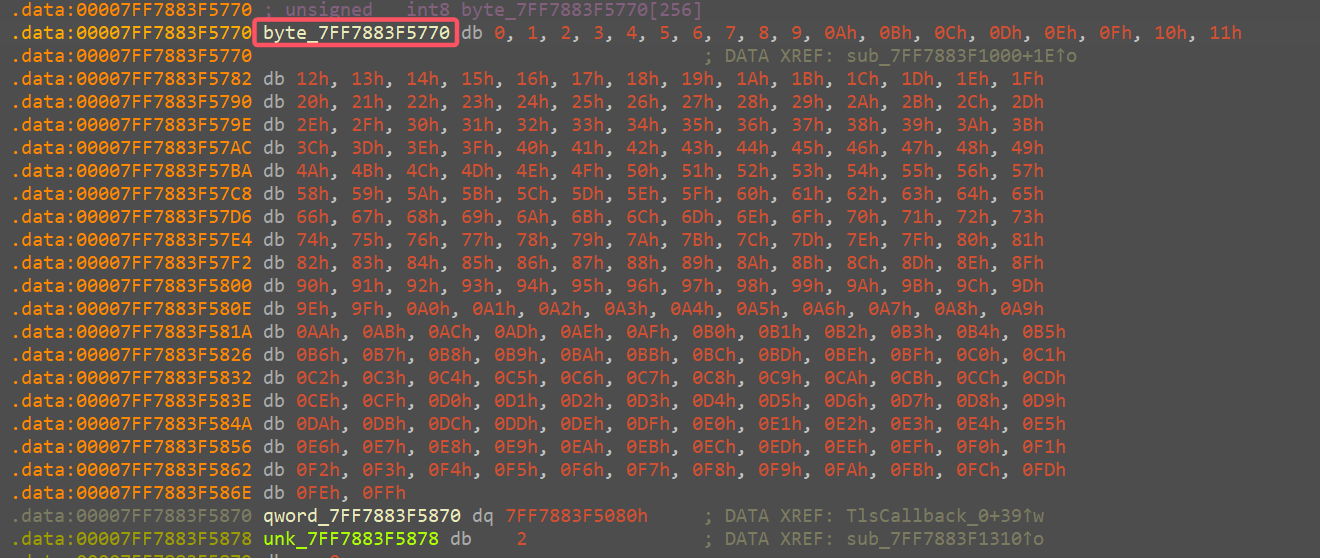
在程序执行时随便输入字符串,进入断点,分别点击aNbgvzyhebfgcv8和byte_7FF7883F5770,得到最终的key
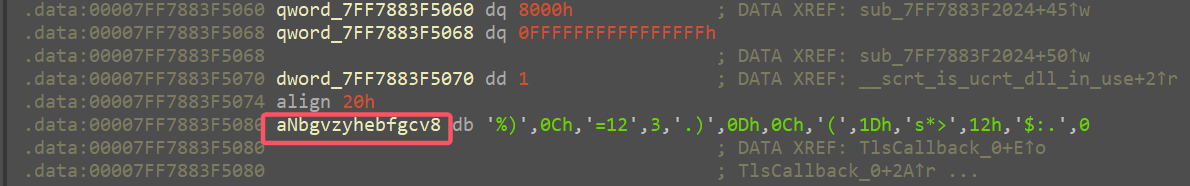
和sbox
3、根据得到的sbox和key,以及main函数的加密逻辑编写exp
key_table = [ |
Flag
flag{590CF439-E304-4E27-BE45-49CC7B02B3F3}
评论