第五届大学生信息安全竞赛-部分WP
Crypto
BASE ALL
题目描述:哇!怎么这么多,搁这套娃呢?
下载文件,打开是一堆编码:
JJFEIRKNKJFUYS2KIZKTIVCDJJGEUQ2VJ5KTEVCLGVDFMRKTGJDEWTSMIVLVIQ2MJJNEIRSNKRFVOS2OIVKVKUSTJJFVURKWI5KTESKKJZBVMVKWKNIEWSK2IRCVEMSLJFHEWVSTKUZEYR2KIVKEWU2TKVFFMSKUIVKEWS2MJJDFMSKSJNLUWTSMIVHVMU2EJFLEIVSJKVNFGSSOJRCUOUSLJRFVKWSFJFJUWS2KIZBVKS2VLJJUWNKGIU2FGMSGJFLEYVKHKRJUQS22IVCUWVBSKZGEUSSVKNKFGRSJKVNEMT2VKNLEUTSOIVKVMQ2MJNGVURSRKNFFMSK2INLE6VKTGJFTKRCVGRJTERSLIZFFIRKRGJFUSWSGKZFVMMSPJNHEGRKXKNJUQS22JNLEGVJSLFFE4RCFKFJFGSSLGVFFKVKTKNFUUVSMIU3FMUSTJNHEKVJUKJFVMSZVJFLEOUSLJRDVMR2GJFKEWVCHJJGEKVKOJNEUSWSGKZHVCMSRJJHEYRKPKJJUYS2OIZKU6VCDI5EVMQ2UIVLEGVCJJZDFIS2SGJLEOUSMKVLVEU2KJNLE4RKJKIZFISKOIZKVKU2TI5EVMSCWIVJTEUCKJZEVMVKSJJJUWWSKIZEVGMSTJE2UYRJWKZFVIR2KIZCTIUSLK5FU4TCGI5KVGSCLLJCEMS2WGJKUOSSIKVKVGU2EJFLEMVSLKMZE2SSKIRCU2USLIZFTKQSVJNJUUVKMJJCEKS2WKNCEUVSGIVKVIS2WJJLEWVSVKZJUQSS2IJKUWTKTKNFU4SCVKNKVGRKLKJDFKMSNKNJEURJSKVGVEQ2GJNNEEVSFKRBUOSK2JNKEKVSDKRFDKRCVKVITEV2JJZEEKR2VGJGEOVSDIZFVMS2TJNHEWVKVJZFU2S2WIRLEKVJSJNFE4RSFKVJFGTCLJVNEMS2TGJHUUSSLKU3FKMSUJNHEMVSNKNFVOSSOI5LEOVJSJREUURCFJVITEV2LJZFEKWKTKNBUSWSIKZDVGMSMJJDEMRJSKJJUIS22IZLESU2KKZEVETCFJNKVGVCJKZCVIS2UJNKUSVSKIVDVKQ2MJRFEEVKNKVFVOSSOJBKVGU2TJNFVKMSGIVKTEVCKJZFEKU2WKNGEWVK2IZGVGU2LJFFEGVKTKZJUIS2KIZKVKUKTI5FVMS2GI5KDETCKJJDFMS2NKNHEWSSLIVLU4S2IJFLEUVJSJVJUQSSGINKEKVSDJBFTKRSVGJJUWS2JLJCEKV2VKJJUYQSGKU2FIU2GJNHEURSHKUZEWSKKIZDEWTKTJZFU4S2VKNHEEU2LKZFFMT2RGJFUUTJSKVKVEU2KJNEVURSPKMZE6SKSINKE2VSLKRFVMRKWIVJEWRSJJZGFKV2XINFEUVK2KVGVEMSYJJHEQVKVKZFTES22I5LE2U2TKVFE4SSFGJJFGQSLJJFFKV2TGJLUSUSMIUZFISSTJM2UMRSNKNBUMSKWJJKUOUSDJRGEURSGJNJUWVKHJJFFKV2TKNGESVJTIZGVCMSVJJJEIRKNKZFVMS2OIJKVCU2LJ5FFEQ2VJ5KUWVCKKJCVMVKTKNLUURSKIVLVOU2LJNFEEVKLJZBVGS2OIVCVOVSTINFVUSCWI5KTEVKKIUZFKU2WINEEWTSCKU2FGMSPJFHEIRSLKZBTES22IZCTIUSDK5ETKSCFK5LEWTCJLJBVMS2WJNMESTSFIVKU4S2MJNLE2VSLKUZFCSSOJZCU2USLJJFUSWSFGZJTEU2JJJFVKNSWKNFUWUSFKRFVGMSXJFLEYRKHKVFUWR2WIVCUWURSKNDUURSFJ5LVGS2JLJDFMR2TGJMEUTSIIUZFES2MJNIVURJSKMZEGSJVJRCTEVKTIREVMRSVJVJUWVSMIZFFMR2UINEEWWSFKZGVKS2TJJFEWVKXKNJU4SKVGJDEKVJSKBFEMTSFJ5LFGTSLJZFFMR2TKNFUUUSEIVJVMU2EJJJEIVSVKMZEOSJVJJLEOUJSJRFEUQ2VJNJTEVKKJZFUKV2OJNEESVSDKZCVCMSHJJJEGVCFKZBUQS2WIZLECU2TGJFFETCGINKTETCLKZDFKNCRGJDEOSSLIZCVMS2KI5IVURKNKNFVGSKNLJCVOUKTIVEVURCWI5ITER2KJZFEKVKWJNNEWTSKKZHVGU2PJFHEWVKXKRJUYSKSIZLE2USLK5EVMTCGI5JDESSJLJDEMS2SGJLUSTSFIVLVOU2IJNNEOVSDJVJVKSJVIZCUSVSLKZFVMSSVI5JVGQ2JJJFUKT2UJNKEWQSFKRFVGQ2GJNHEYRSVKUZE2SSGJZDE2U2LKNDUSWSFJ5KFGTKLKZEFMT2TLJJUUUSGIVIVMSSVJNGVURSFKNBVMR22JNCEKVKDJJEFKPJ5HU6T2PI= |
放进CyberChef,看到最后的一个=,先用base32解码解4次,得到了:
BHFgBMg4QRUjtBi47cgDZ2ixKm5Ztbnh2HAxUUL7gZihGfyYuV2TongPQExQfCh6yBqkDHPGkyTsiwQtApv46cpBkgJRb6zew6Z9R1XuJsR2AHHn3j3ZpYwcaZ3wo2u8aLktHr62K7XEDcENR2cHSQzaXd6BCxRF4J3cCuGz42ic8RTHG8D9kcFkvZ6PwxXSCZYAby3S7QtZ35dWFc81azXk7ZnwySCWucBqVCtc7NXRNaTAQe2aciMAY246vHywTivpBngQquR36b56jFosDdz4Eer9oeF8AiWarr7iZVU1Mg5zrHbr2VXFLwpsmtNCcxnLyydrNKMTBtTDjPHS5YQKFLBqoN3Qmgs6wcc9sU |
没一个或者两个=,说明不是64或者32,都尝试一下,得到是base58,用其解码4次:
VmpCV1IxWnNXa1pVYkZaVFltNVNWVlJWV1RWbGJVbDRUMVpTVGxKcWJEQlVhMk14VjJ4bmVsVnJjR2xXTVZvMlUxWm5kMUJSUFQwPQ== |
两个=,说明是base64,最后解4次码得到flag:XAUTCTF{S0_so_S0_m4nY_tImes!}
RSA Level 1
题目描述:摊牌了,全给你吧!
下载附件,
from Crypto.Util.number import * |
是最经典的RSA,给了p、q、c,e=65537,直接写exp:
from Crypto.Util.number import * |
RSA Level 2
题目描述:如果N相同,咋办呀
打开附件:
from Crypto.Util.number import * |
给了两个c和两个e,e1和e2,c1和c2,还有一个共同的N,结合RSA相关,知道是共模攻击
核心思路是利用扩展欧几里得算法,求s1&s2,用m = (c1^s1 * c2^s2) mod N解得最后的flag。
exp:
from Crypto.Util.number import * |
Hello Elgamal
题目描述:你知道基于DLP的是什么加密算法吗?
打开附件:
from Crypto.Util.number import * |
结合题目elgamal知道是elgamal的公钥加密,其中p是大素数、g是生成元、y = g^x mod p是公钥,x是私钥,计算c1和c2。
核心的解码公式是s = pow(c1, x, p)和m = c2 ^ x,
我们通过暴力破解得到x,利用XOR来得到最终的flag,exp采用多进程来提高爆破效率。
exp:
from Crypto.Util.number import long_to_bytes |
Reverse
JS_Enigma
题目描述:
啥也不会的debu8ger一个寒假没碰自己的博客,开学打开发现了一个神奇的网页! 请你定位到这个网页并收获属于你的first egg! 博客地址:https://incldue.github.io/
提示:flag在/flag
点开博客,根据提示直接拼接命令进入/flag.html,是一个flag加密界面:

按F12查看源代码,得到核心加密逻辑:
var key = 6; |
将明文用6进行异或得到Cipher,解密直接逆着异或来得到原始flag:
cipher = "^GSRER@}R6jbYSYluYui6i6YC|||'{" |
EzPy
题目描述:深夜一条披着羊皮的小蛇溜进了农场主的农场里, 请你找到这条小蛇并获得你的奖励吧!
根据题目,知道是用python打包的.exe文件,于是将exe文件解包,得到一堆东西
找到有和原文件同名的.pyc文件,用在线网站PyLingual反编译:
import base64 |
整个流程就是将flag用Gen(key)生成的50字节密钥进行逐字节的XOR,然后再用base64编码得到密文。
有S盒,说明是改造版的RC4加密,用key = 'welcome_to_our_5th_xautctf'循环打乱S盒;PRGA算法生成密钥,XOR加密,最后base64编码。
最后的exp就是把以上过程逆着来一遍:
import base64 |
test your asm
题目描述:来学习一下好玩的asm嘛?
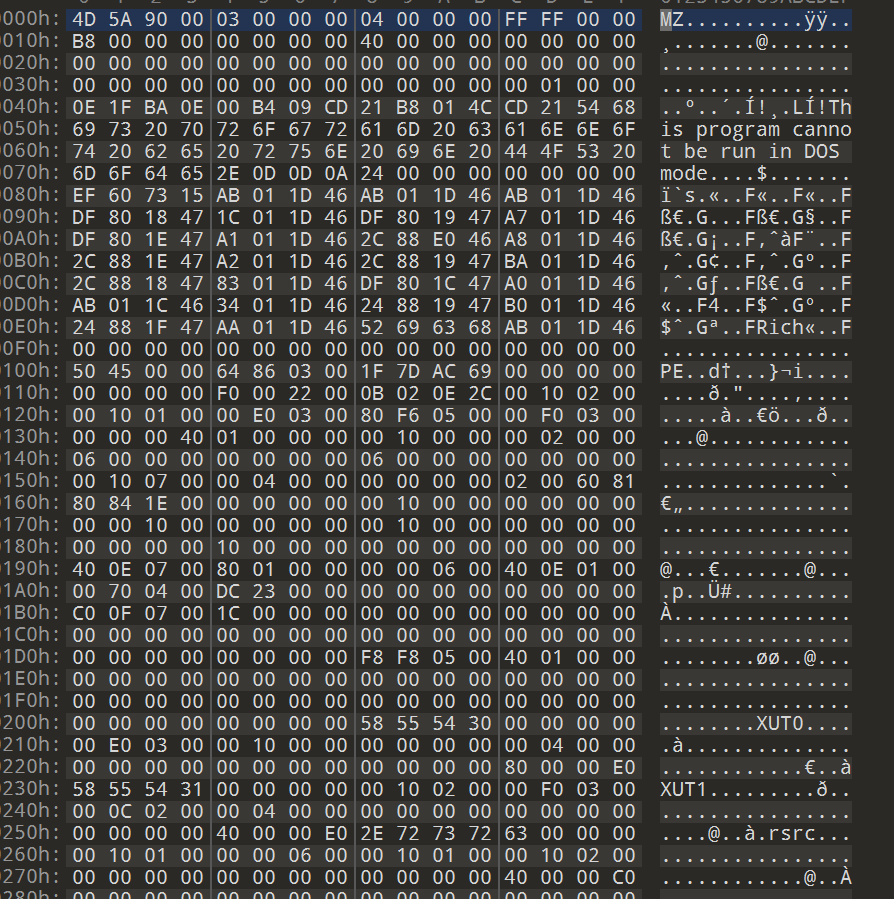
下载附件,在DIE里检查:
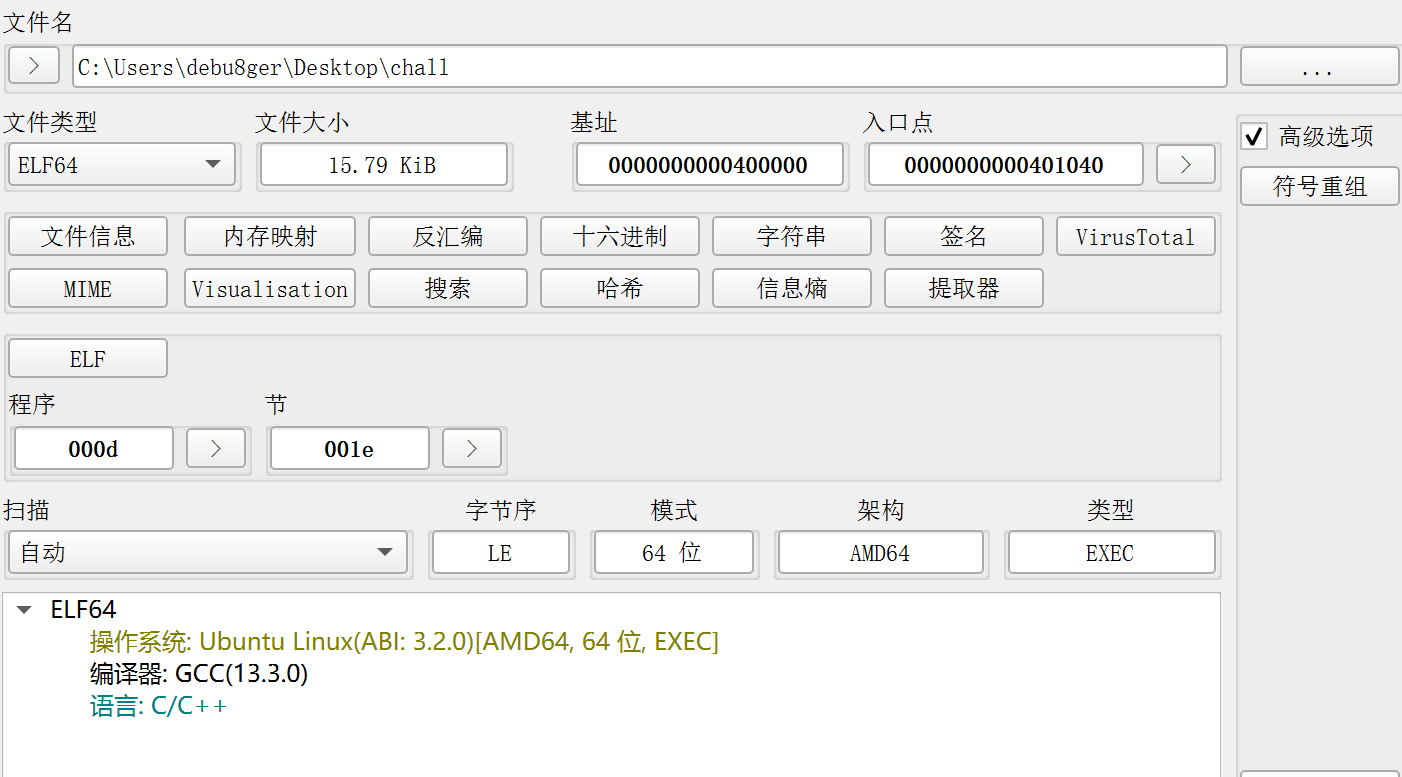
是64位ELF文件,无壳,IDA打开
main函数即为主逻辑,
{ |
将flag与0x13异或后循环左移3位,再异或0x37得到密文。
点进d1数组查看,发现一连串数据,即为密文数据
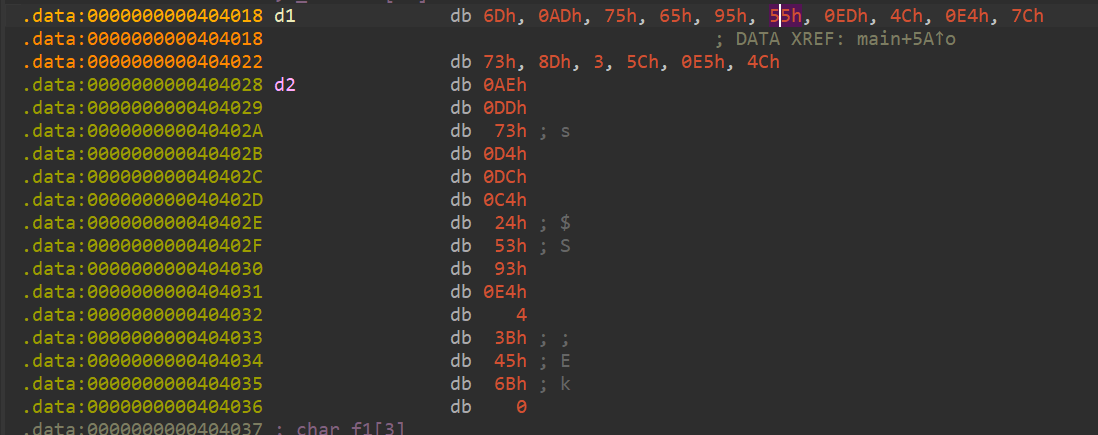
最后exp:
cipher = [ |
EzTea
题目描述:请你喝一杯淳朴的茶 ~~
[这题本来想考察TEA加密的,但是点进数据转hex可以直接出flag,这题没出好,我的错,道歉了 :( ]
老习惯,下载完DIE一下,
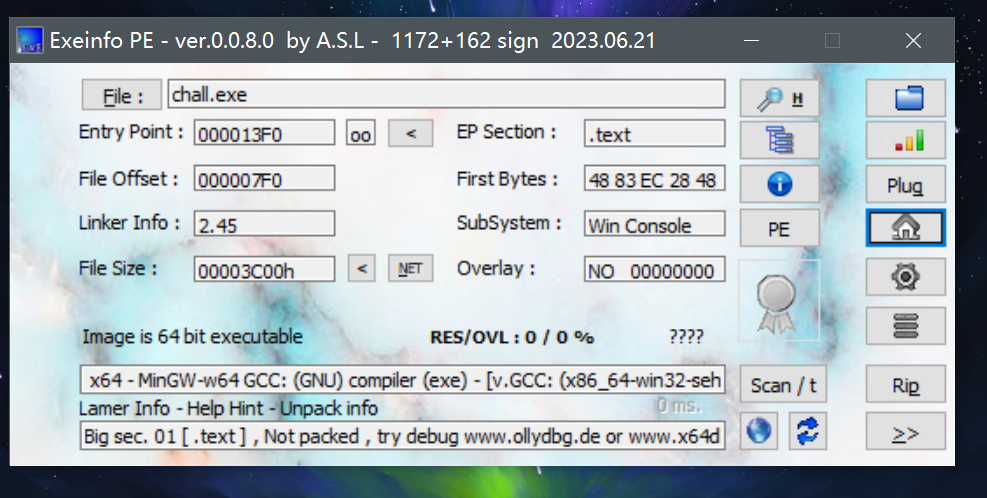
没加壳,64位可执行文件,再IDA打开,
主函数入口在sub_140002900,
__int64 sub_140002900() |
v5数组存储密文,函数sub_140001440对应TEA加密,
v2 = *a1; |
每次对64 bit的数据块进行32轮运算,key为128 bit,
通过对常数进行进制转换,得到了常数0x6A09E667,为TEA算法的经典特征
对v2 += F(v6, sum, key)和v6 += G(v2, sum, key)进行32轮逆运算得到flag
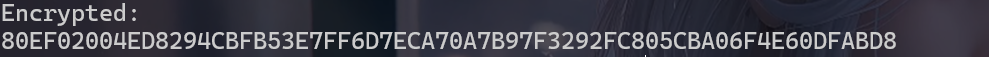
密文则是通过运行程序得到:
所需的key在数据xmmword_140004010中,
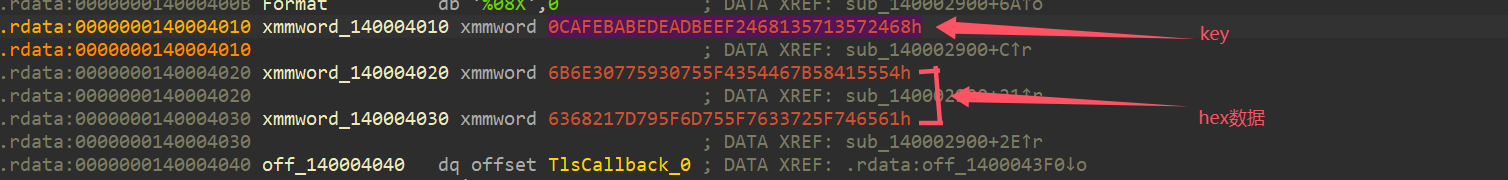
编写最终exp:
import struct |
贪吃蛇…吧
题目描述:你玩过贪吃蛇吗? 听说达到了50000分的勇者可以获得一把屠龙宝刀哦~
提示:想想UPX的特征呢
照例,DIE一下,
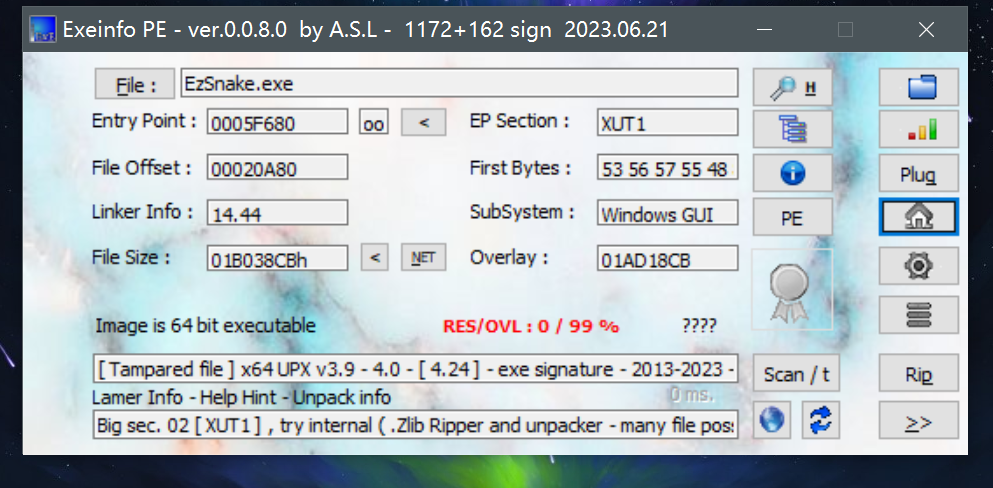
64位可执行文件,有UPX压缩壳,用UPX尝试脱壳,显示错误
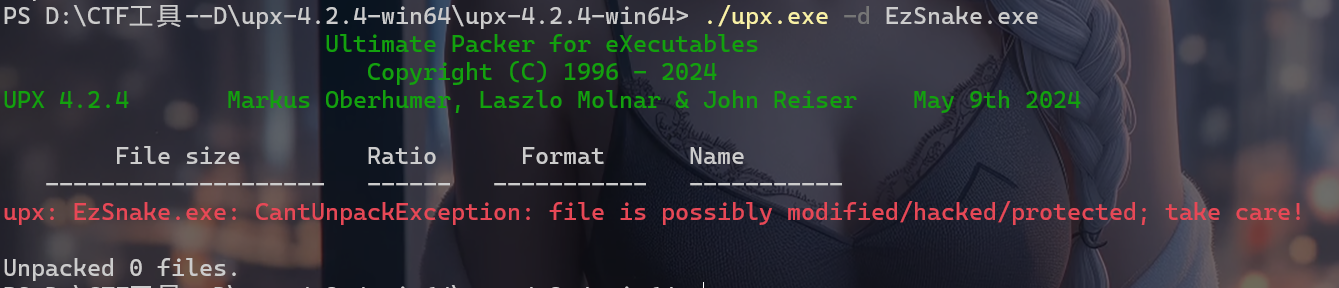
于是在010里面查看hex详情,
可以看到在原本UPX特征位上的UPX字符不对,所以我们选中XUT,将其修改为UPX,替换所有的XUT,然后再进行UPX的脱壳,成功脱壳,得到原文件
点击,是贪吃蛇的游戏,根据题目猜测得打满50000分才能获得flag
用IDA打开,查看字符串发现有Py...样式的字符,推测可以用python解包,
于是跟上面EzPy一样的操作解包,在在线网站反编译,直接得到了源码
import random |
可以看到一眼假的flag,下面的便是真正的密文,有8个32bit整数,4个TEA加密块
后面的密钥生成依赖于你所得分数和最终蛇的长度
后面有TEA加密常数0x9E3779B9,进行32轮的解密
第二层是一个链式的XOR,res[i] ^= res[i - 1],解码只需逆着来
要解码,我们得估算到50000分时蛇的大概长度,当然也可以暴力破解直接拿到估计长度,逆向算法后通过暴力枚举参数来获得50000分时的长度。
最终exp:
import struct |